TL;DR
- Security teams are already building AI agents to cover headcount gaps, but coverage stops at whatever each one can reach, and the stitching still falls on the agent itself.
- Sola’s MCP and Slack AI agent give any agent or client one connection to your full environment: identity, endpoints, cloud, SaaS, threat intel, and code tools, all federated.
- Single-product MCPs answer from one tool; Sola’s returns one correlated answer with the relationships intact.
- Live today on the free tier in Claude, Cursor, VS Code, Claude Code, OpenAI Codex, Slack, and any MCP-compatible custom agent.
Six months ago, we argued that MCP didn’t solve the core problem for security teams. The argument still holds.
Building your own security agent is the right move. Lean teams are already doing it. The grind is wiring that agent into unified context across the stack. The Sola MCP Server is live now, with a free tier, sitting on a federated intelligence layer that already does the wiring.
What we said six months ago
The original critique was structural. A single-product MCP wraps one tool’s API. An AWS MCP knows AWS, an Okta MCP knows Okta, and neither sees how the two connect in your environment. The analyst, or the agent calling them, stitches by hand.
The longer argument lives in that post, and the point still stands. It was written in response to vibe coding going mainstream, and the rush that every vendor joined to wire their own AI hookups. Security teams ended up with more endpoints to query and no less stitching work to do.
Today, Claude, Cursor, VS Code, Claude Code, OpenAI Codex and others all speak the protocol, and security teams are using them for operational work. The leanest are already running internal agents to compensate for headcount gaps, wiring them into whatever data sources they can reach. The problem is that reach is still limited by what each tool can see on its own.
What Sola’s MCP sits on
Solving that reach problem is what this MCP launch is about. The question stopped being whether to use MCP and became what to put under it.
That’s where Sola’s MCP comes in. Most MCP servers wrap one tool’s API, which works when the question lives in one place. Even when teams wire multiple MCP servers into a single agent, the problem doesn’t disappear. Each MCP represents one system with its own schema and no awareness of how it relates to the rest of the stack. The agent still has to stitch partial answers together, which adds coverage without adding a correlated picture of the environment.
Sola’s MCP takes a different approach: it federates across security domains, pointing at a shared intelligence layer that already reasons across identity, endpoints, cloud, SaaS, threat intel, and code tools together.
One query reaches all of them. One answer comes back, with the relationships between sources still attached, instead of five partial ones to reconcile.
Find out how to connect in our Docs.
Security answers where the work happens
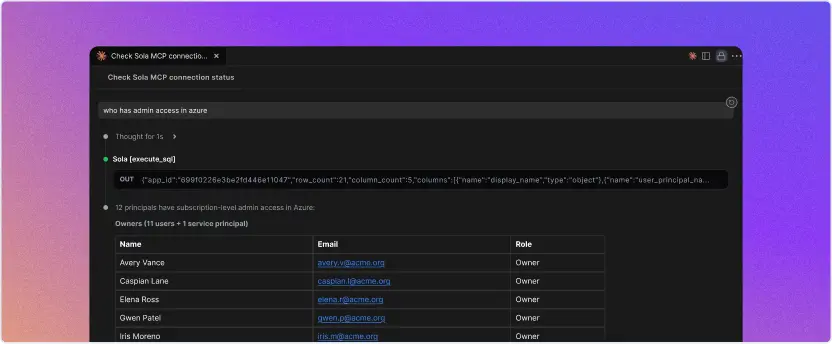
The Sola MCP and Slack AI Assistant bring this layer to the surfaces your team and your agents already work in. The practical difference shows up in the depth of questions you can actually ask in Claude or Cursor with Sola MCP connected: “Which critical findings affect production services owned by team X, and who has admin access to the underlying infrastructure?”
A unified, cross-domain layer like Sola’s sees all of it in one query, where a single-product MCP would stop at its own boundary and hand the rest back to you.
Stay in the tools you already use
Security teams often manage dozens of tools and cannot afford to jump between dashboards. So Sola’s MCP meets you in the tools you’re already in:
- Cursor mid-PR: A security engineer checks whether a service has open high-severity findings without leaving the editor.
- Slack permission check: A lead verifies whether a contractor still has production access without leaving the thread where the question started.
The answer comes back from every connected source, ranked by risk, with relationships intact. Meet Sola in Cursor, Claude, Slack, your IDE, or any other MCP-compatible tool.
The AI agent gets the whole picture
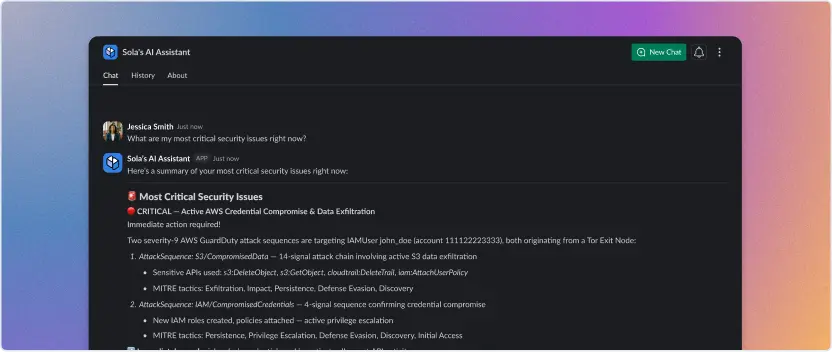
The biggest payoff lands in the agent layer. Lean security teams build agents to cover work they cannot hire for. These agents bring their own reasoning, yet they only know what they can reach.
One connection to the Sola MCP gives an agent access to every connected source, vendor table, and graph relationship in the environment. A triage agent can check whether an affected service is internet-facing, who has admin access, the data sensitivity levels, and whether related tickets are open. This all happens in a single call. Coverage scales without headcount scaling with it, and without the credential sprawl and integration overhead that comes with wiring each agent into every system separately.
Sola MCP: security and agent governance built-in
Our original MCP critique called out the real risks of running MCP in security: prompt injection, over-scoped tokens, weak schemas, untracked drift. Those risks haven’t gone anywhere, and as teams build more internal agents, a second problem compounds: access sprawl.
Without a unifying layer, every agent needs its own credentials, its own permissions, and its own audit surface for every system it touches. Each new agent becomes another identity to provision, secure, monitor, and track. Wire enough of them and the agents themselves start looking like an attack surface..
Sola changes that model. Agents connect to Sola once, and Sola handles the underlying access to every connected source: read-only by design, with identity binding tied to the user calling it, strict trust controls on every connected source, input and output sanitation, and full logging of every query and response.
Sola’s MCP keeps the human in the loop on purpose. The agent builds the clearest picture of your environment as fast as possible, and the decisions around what to do next stay with the person reading the answer. What to revoke, what to escalate, what to merge, what to deprioritize: those calls don’t belong to the agent.
All of this is available today, on the free tier.
Try Sola MCP on the free tier
A single-product MCP answers from one tool. Sola’s MCP answers from your whole stack.
Connect Sola’s MCP in Cursor, Claude, or Slack on the free tier, and ask one question across your full environment. You’ll get back one correlated answer with risk ranking and source relationships included.
The agent or analyst doing the asking does the next part.
Connect the Sola MCP wherever your team works.
Frequently asked questions
VP Product, Sola Security
Shlomi has led product at Palo Alto Networks, Cider Security, and Illusive Networks. At Sola, he takes messy, complex security problems and turns them into a product people actually want to use — and spices it up with sarcastic one-liners exactly when the room needs it most.