TL;DR
- Shadow AI has expanded from browser tabs to identity platforms, SaaS apps, endpoints, code repositories, and cloud infrastructure, and single-layer detection tools only see fragments of the picture.
- Gartner found that 69% of organizations suspect or confirm employees use unauthorized AI tools, but most detection approaches cover only one surface.
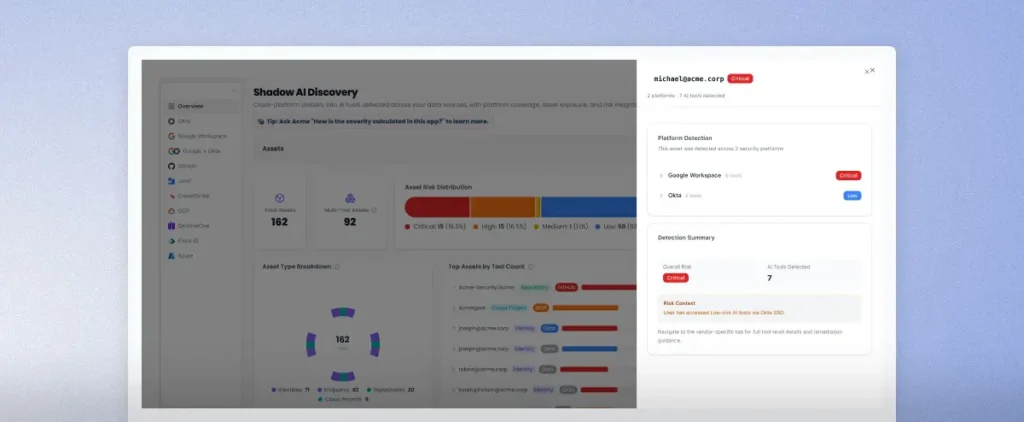
- Sola’s Shadow AI Discovery app cross-correlates findings across 10 data sources, turning disconnected signals into severity-scored, prioritized findings with remediation guidance.
- Connect your existing data sources and get a full shadow AI assessment in minutes. The app is free to try.
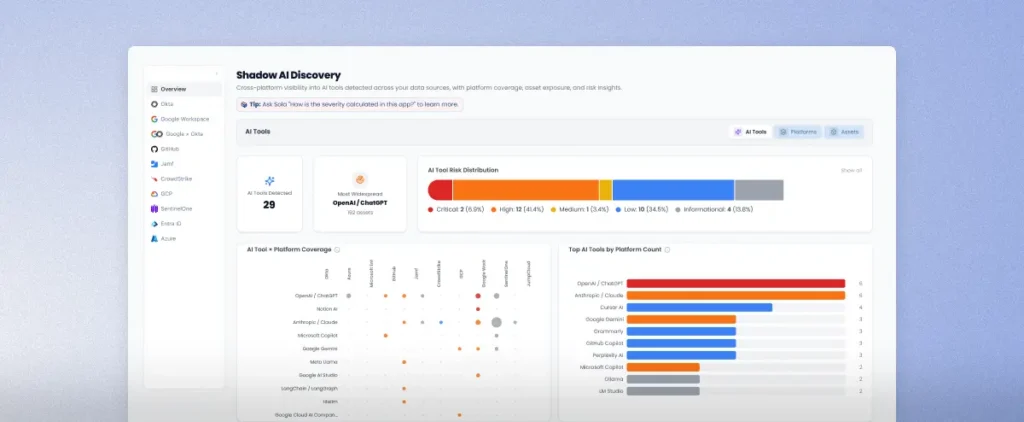
Connect your data sources, run the Shadow AI Discovery app, and within minutes you’ll see which AI tools live across your connected data sources, each one severity-scored from Critical to Informational. Most security stacks can’t produce that view, because no single tool covers all the layers.
We built the app to answer the question most CISOs recently brought to RSAC 2026: where shadow AI actually lives across identity, SaaS, endpoints, code, and cloud.
Get the shadow AI discovery app.
Sign up and grab the app from the App Gallery.
Shadow AI moved past the browser tab
A year ago, shadow AI meant employees opening ChatGPT in a browser tab. Since then, the scope has expanded well beyond that.
Employees now sign into AI tools through Entra ID and Okta, authorize OAuth access to Google Drive, install desktop clients like Cursor and Claude on company laptops, embed AI libraries in code repositories, and spin up Vertex AI or Azure OpenAI services inside cloud projects. Five layers of AI adoption, each creating a different data exposure path.
Shadow AI covers any AI behavior in your organization that you can’t see or control. And risk can also live inside integrations your team already reviewed and approved: the OAuth connection your CISO greenlit, the Google Drive plugin that went through IT’s standard vetting, the AI coding assistant your engineering team adopted with full procurement sign-off, and the Slack bot that indexes conversations to feed an LLM summary feature.
CrowdStrike acknowledged the shift in March 2026 when it extended Falcon’s runtime detection to desktop AI apps. The company noted that desktop AI tools look nearly identical to legitimate user behavior on developer machines. And browser-based usage, which most monitoring tools still focus on, is now only one piece of a much larger problem.
And these layers compound. An employee installs an AI tool on a managed laptop, connects it to Google Drive via OAuth, but signs in with a free-tier personal account outside the organization’s control. Your EDR sees the install, Google Workspace logs the OAuth grant, but the actual usage flows through an unmanaged AI account that’s harder to catch. Each tool in your stack sees its own slice, and none of them show the full picture of that AI tool’s footprint across your environment.
Each of those layers carries its own risk profile. But for this article, we’re going to zoom in on the one that affects virtually every organization: the native SaaS-to-AI integration. It requires no technical skill to set up, follows a standard OAuth flow that feels routine, and as we discovered firsthand, it can create data exposure that’s invisible to traditional monitoring.
Single-layer detection never accounted for a five-layer problem, and the gaps between layers are where compound risk builds.
What single-layer detection misses
Most shadow AI detection approaches focus on a single surface: browser activity, OAuth tokens, or endpoint installs. Each one catches something real. The problem is what each one misses.
A browser monitor flags an employee visiting an AI tool but can’t tell you whether that tool also has OAuth access to company data. Your SaaS security stack spots the OAuth token but has no view of the desktop client sitting on the same user’s laptop, or the AI library embedded in a CI/CD pipeline three repos away.
Gartner’s 2025 survey of 302 cybersecurity leaders found that. The word “suspect” is worth pausing on. When your detection tools only cover one layer, suspicion is often the best you can do, because you’re seeing fragments without enough context to act.
And the operational cost adds up fast. The same AI tool might appear as a low-priority OAuth alert in one console, a medium-severity endpoint finding in another, and an informational sign-in log in a third, with nothing connecting them. Security teams either chase each fragment manually or, more likely, deprioritize all of them.
Turning those fragments into a single, severity-scored finding requires pulling data from all five layers at once. We built the Shadow AI Discovery app to do exactly that.
What the shadow AI discovery app surfaces
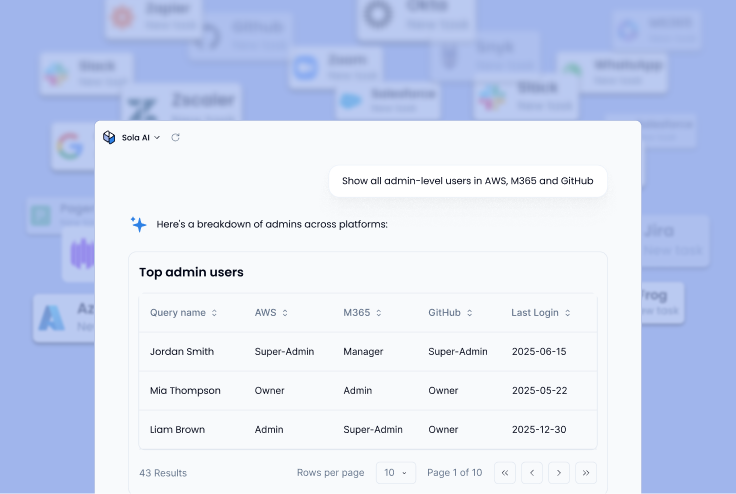
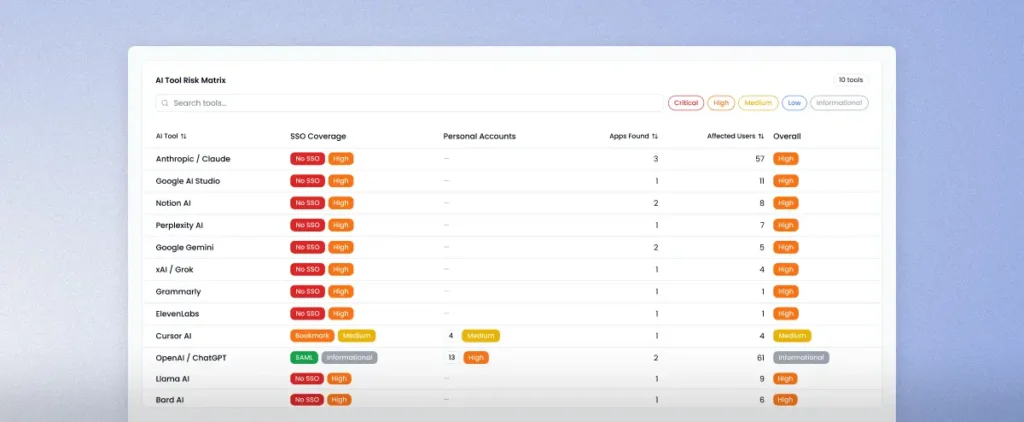
The app covers 10 data sources and answers five questions about every AI tool it finds: which tools are in use, who’s using them, what access they have, whether that access is governed, and what risk each scenario presents. Every finding includes severity context and specific remediation guidance.
Identity and access (Entra ID, Okta, JumpCloud)
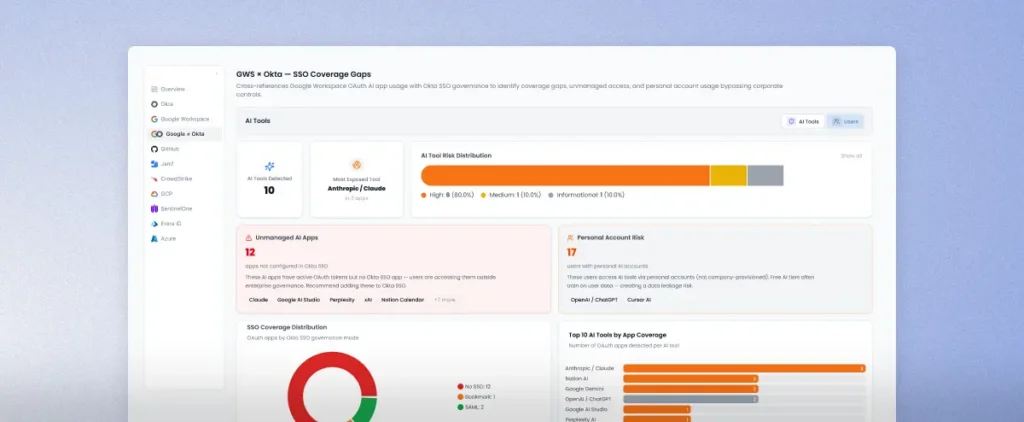
The app shows which users sign into AI tools, where they sign in from, and whether Conditional Access policies cover those sign-ins. Sola catches behavioral anomalies like brute force attempts and impossible travel targeting AI app endpoints, and classifies each tool’s SSO governance mode so you can see which AI apps are federated, which are bookmarked, and which have no SSO coverage at all.
SaaS and OAuth (Google Workspace)
Every AI tool’s OAuth token gets scored by scope breadth, from Critical for admin and directory access down to Low for profile-only permissions. The app also monitors new AI tool authorizations as they happen and flags suspended users who still hold active tokens, a common blind spot after offboarding.
Endpoints (CrowdStrike, SentinelOne, Jamf, JumpCloud)
Across the four endpoint platforms, the app detects installed AI applications, browser extensions, and local LLM runtimes like Ollama and LM Studio. Sola maps CVE vulnerabilities to installed AI tools and rolls up device-level risk with flags for adversarial tools and data sovereignty concerns.
Code and DevOps (GitHub)
Sola scans repo manifests for AI library dependencies and scores CI/CD workflows for AI tool signals. The Shadow AI discovery app also catches AI API secrets stored in GitHub Actions variables, a risk that escalates sharply in public repositories.
Cloud (GCP, Azure)
AI services provisioned without diagnostic logging or network access controls surface immediately. The app covers both managed platform services like Vertex AI and Azure OpenAI and serverless workloads running in Cloud Functions and Cloud Run.
Each layer produces severity-scored findings on its own. But correlating them across sources is what turns fragments into a prioritized risk story.
Cross-source correlation changes the picture
Detection across five layers is useful on its own. The app’s most distinctive capability is what happens when it connects findings across sources.
The SSO Coverage Gap analysis cross-references every AI tool found in Google Workspace against Okta’s app catalog. You immediately see which AI tools have active OAuth tokens but no corresponding SSO governance, which users access AI tools through personal accounts that bypass enterprise controls, and which tools are fully federated. One view tells you exactly where your SSO coverage has gaps.
The AI Tool Risk Matrix takes it further. Sola maps each tool against every detection source with severity. You can see at a glance which tools appear across the most platforms and where the highest-severity findings cluster.
And per-identity risk rollups let you drill from tool-level findings down to individual users, showing how many AI apps each person accesses, across which platforms, and at what combined severity. Security teams go from “we found dozens of AI tools” to “these five users carry the highest compound AI risk” in a single view.
Speed matters here, because shadow AI adoption doesn’t wait for security reviews to catch up.
From detection to decisions in minutes
Most shadow AI projects start with a months-long integration effort: connect data sources, normalize schemas, build dashboards, tune alerts. By the time the first report lands, employees have probably already adopted a dozen new AI tools.
The Shadow AI Discovery app skips that cycle. Connect your data sources (Okta, Entra ID, Google Workspace, CrowdStrike, SentinelOne, Jamf, JumpCloud, GitHub, GCP, Azure), run the app, and get a prioritized view of shadow AI exposure across your environment. You skip the months-long implementation timeline and the dedicated team to maintain it.
Risk classification follows a tiered severity model that scores each AI tool based on its actual risk profile. Geopolitical risk tools like DeepSeek and other providers subject to PRC data governance laws score highest, alongside adversarial tools like WormGPT and FraudGPT that exist specifically to bypass safety guardrails. Mainstream productivity tools like Grammarly score at the lower end. And every finding comes with specific remediation context, so your team knows whether to block via Conditional Access policy, add the tool to Okta SSO, or review and validate the authorization.
The detection catalog keeps growing, too. Sola continuously adds data sources, expands the list of tracked AI tools, and builds new detection capabilities as the shadow AI surface area shifts.
For security teams that have been stitching together shadow AI visibility from browser logs and OAuth audits, the difference is immediate. You go from assembling fragments across five consoles to a complete, severity-scored picture in one place.
See your shadow AI exposure
If AI visibility is the gap that CISOs keep naming, now there’s a way to close it in minutes. Connect your data sources, run the Shadow AI Discovery app, and see exactly which AI tools live in your environment, who’s using them, and what risk they present.
Get a complete map of every AI tool in your environment.
Key Takeaways
- Shadow AI now spans five layers (identity, SaaS, endpoint, code, cloud), and each layer creates data exposure paths that single-surface tools miss.
- Cross-source correlation turns disconnected alerts into compound risk findings, so security teams can prioritize users and tools by actual severity instead of chasing fragments.
- The Shadow AI Discovery app delivers a full shadow AI assessment across 10 data sources in minutes, with tiered severity scoring and remediation guidance for every finding.
- The app is free to try: connect your sources, run the app, and see what’s in your environment.
Frequently asked questions
Security Innovation Engineer, Sola Security
Tal blends a sharp analyst’s mindset and experience with a flair for creativity, crafting security insights and dashboards using Sola. As a Security Innovation Engineer, she even built a Harry Potter themed AWS security app with flying owls and IAM houses, proving security can be both powerful and magical.