See the identity risk your IdP misses
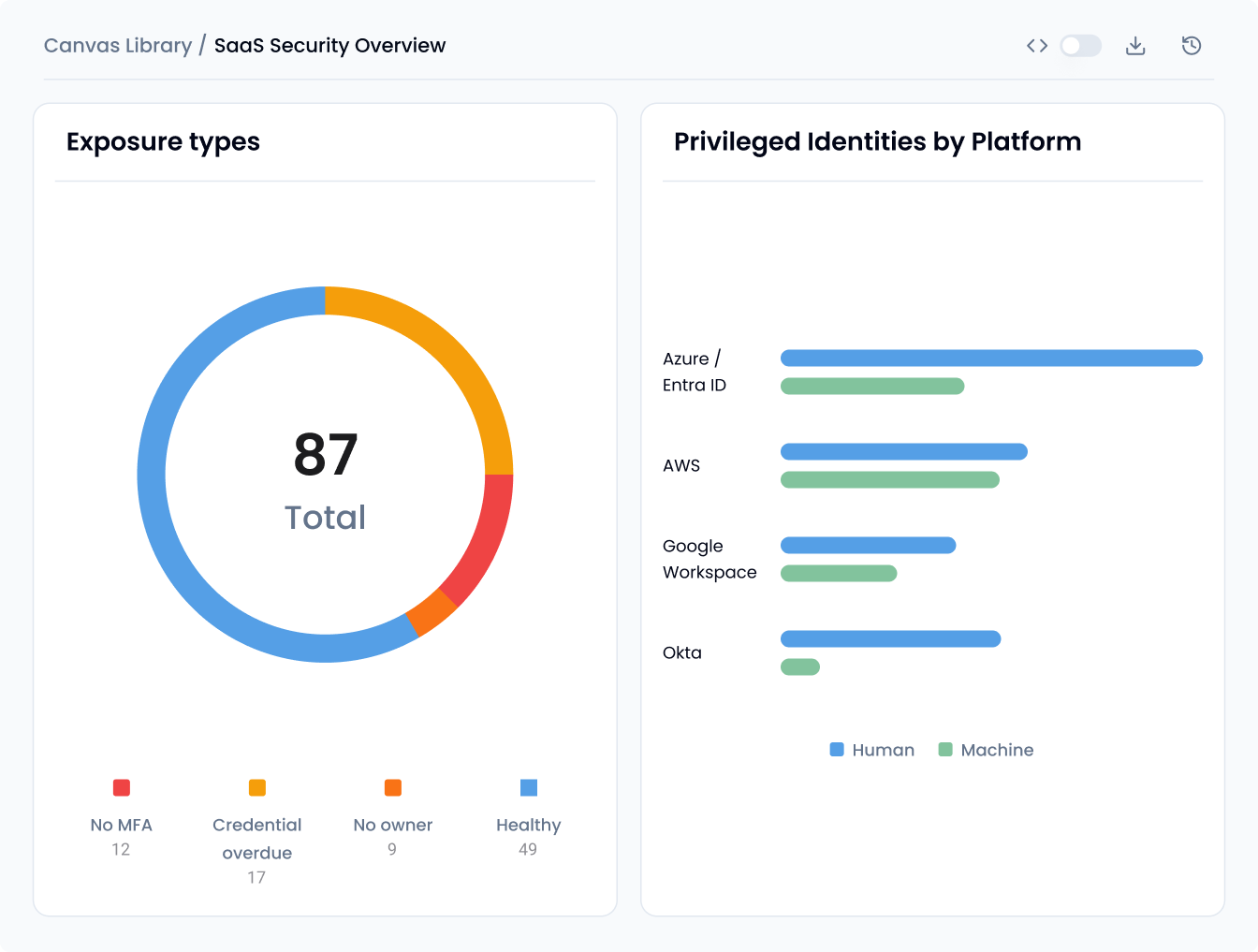
Your IdP centralizes identity and access policies. But shadow admins, orphaned tokens, and toxic permission combos hide in your cloud, SaaS, and everywhere your IdP doesn’t govern. Sola connects your identity data across the stack, so you see effective access and fix gaps – in minutes.
Solve the identity chaos, fast
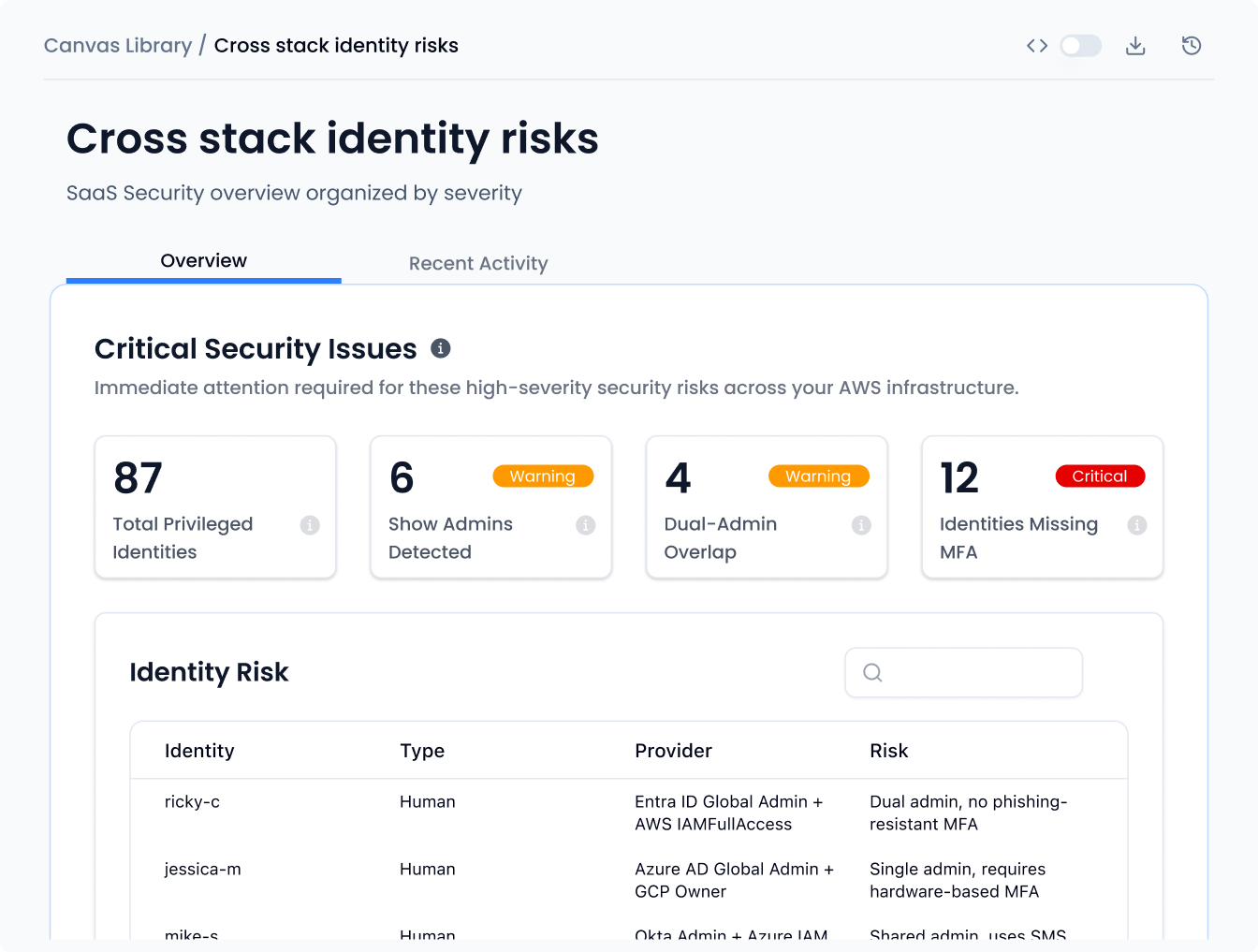
Stop stitching together access data from five different consoles. Sola lets you ask the hard questions across your entire identity stack and get actionable answers you can share with stakeholders immediately.
Review cross-stack privileges
Hunt toxic combinations
Tighten loose permissions
Export audit evidence
Purge orphaned accounts
Prompts to get you started
How Sola works:
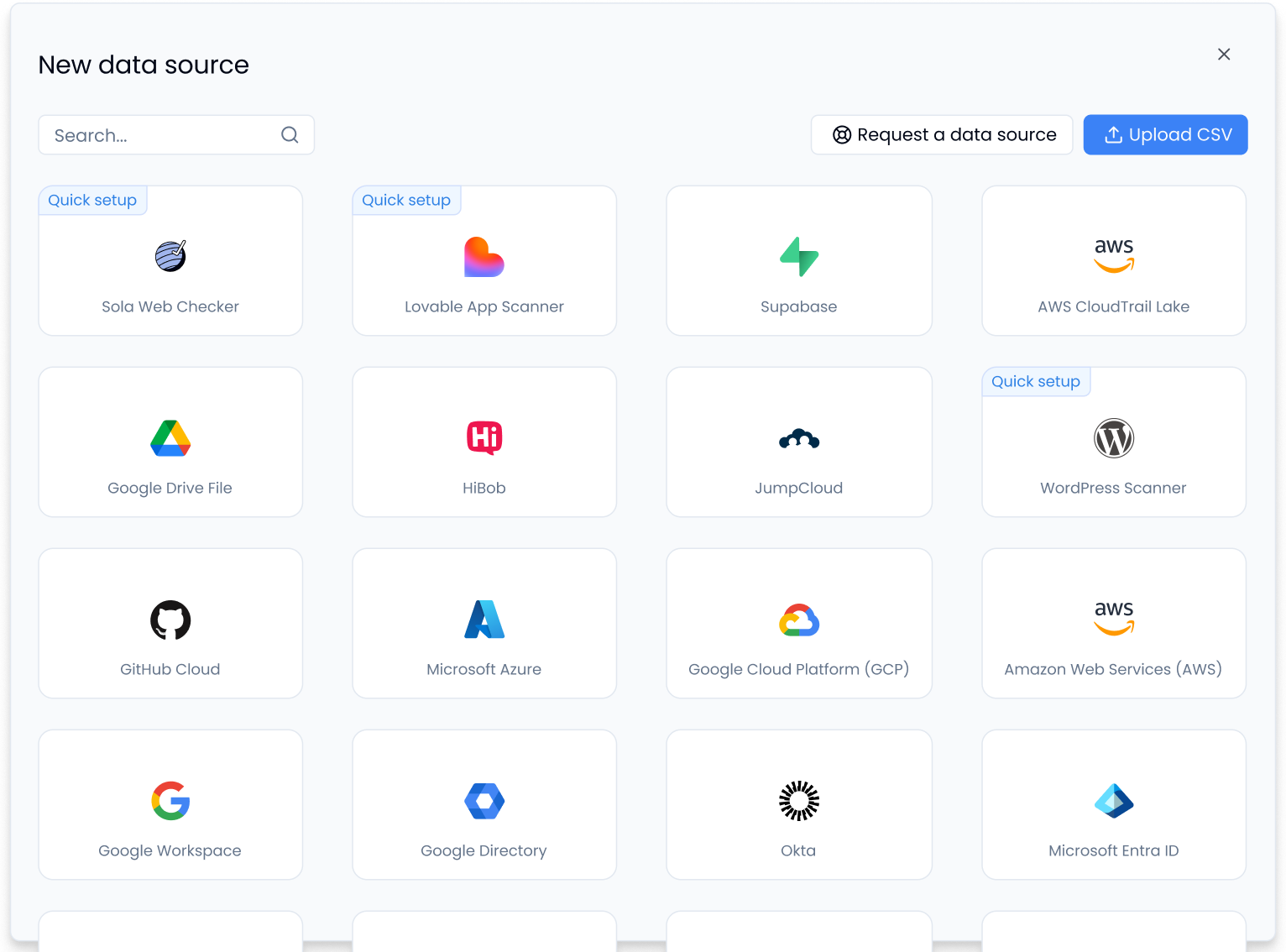
Connect your identity sources
Connect your IdP, cloud accounts, and SaaS apps in minutes. Sola pulls identity data from Okta, Entra ID, AWS, Google Workspace, and more, then normalizes everything into a unified graph. No agents required.
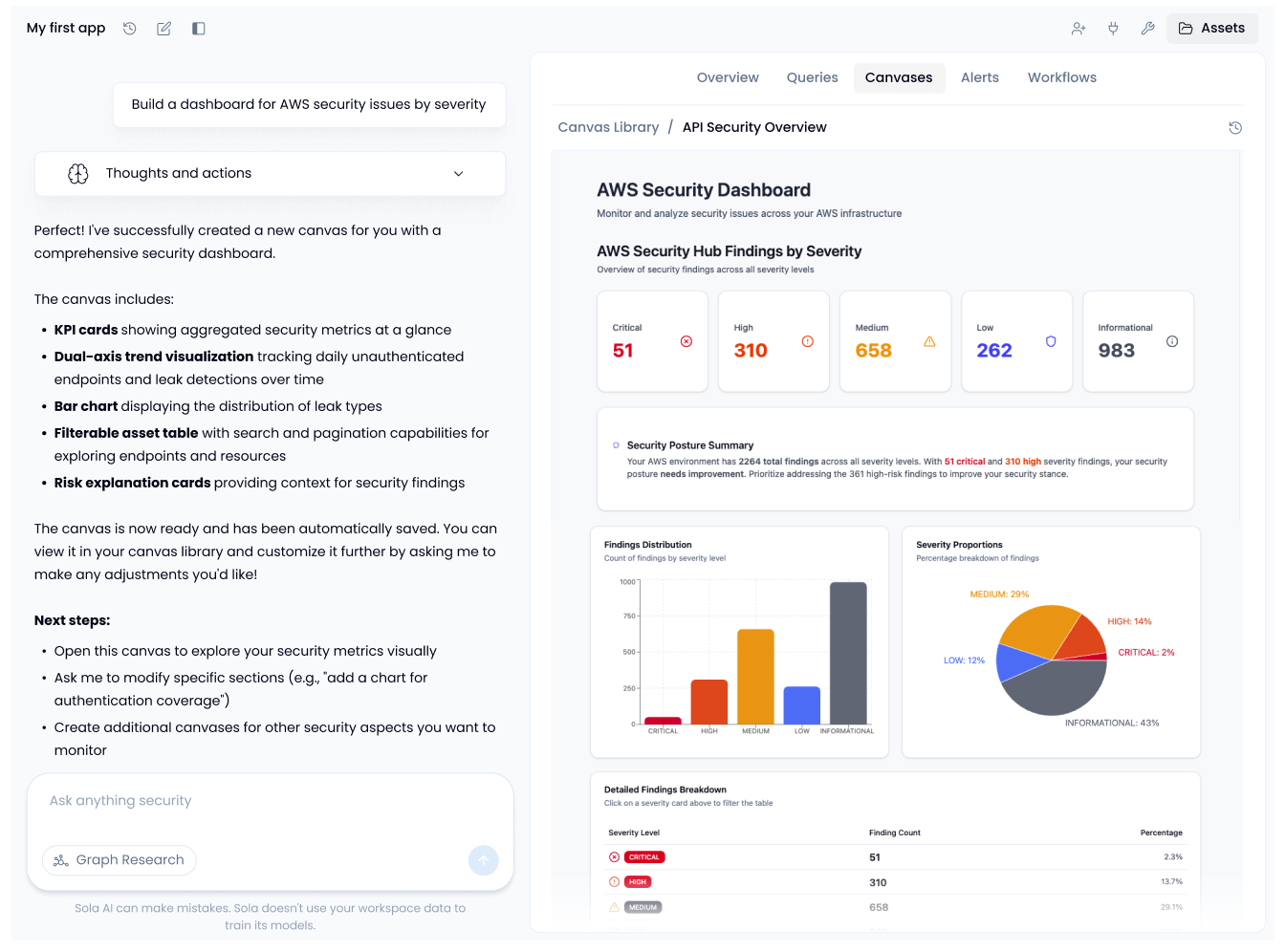
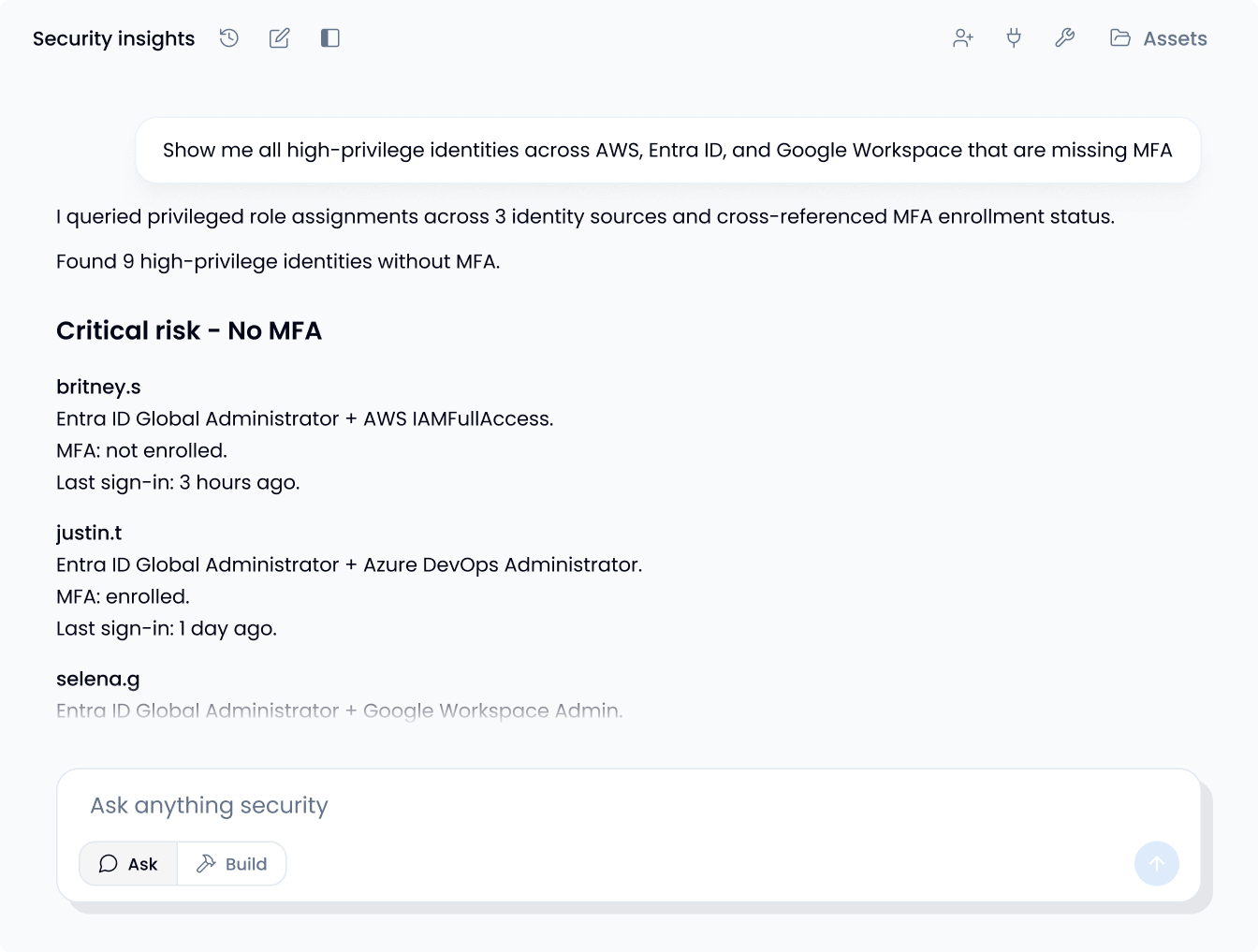
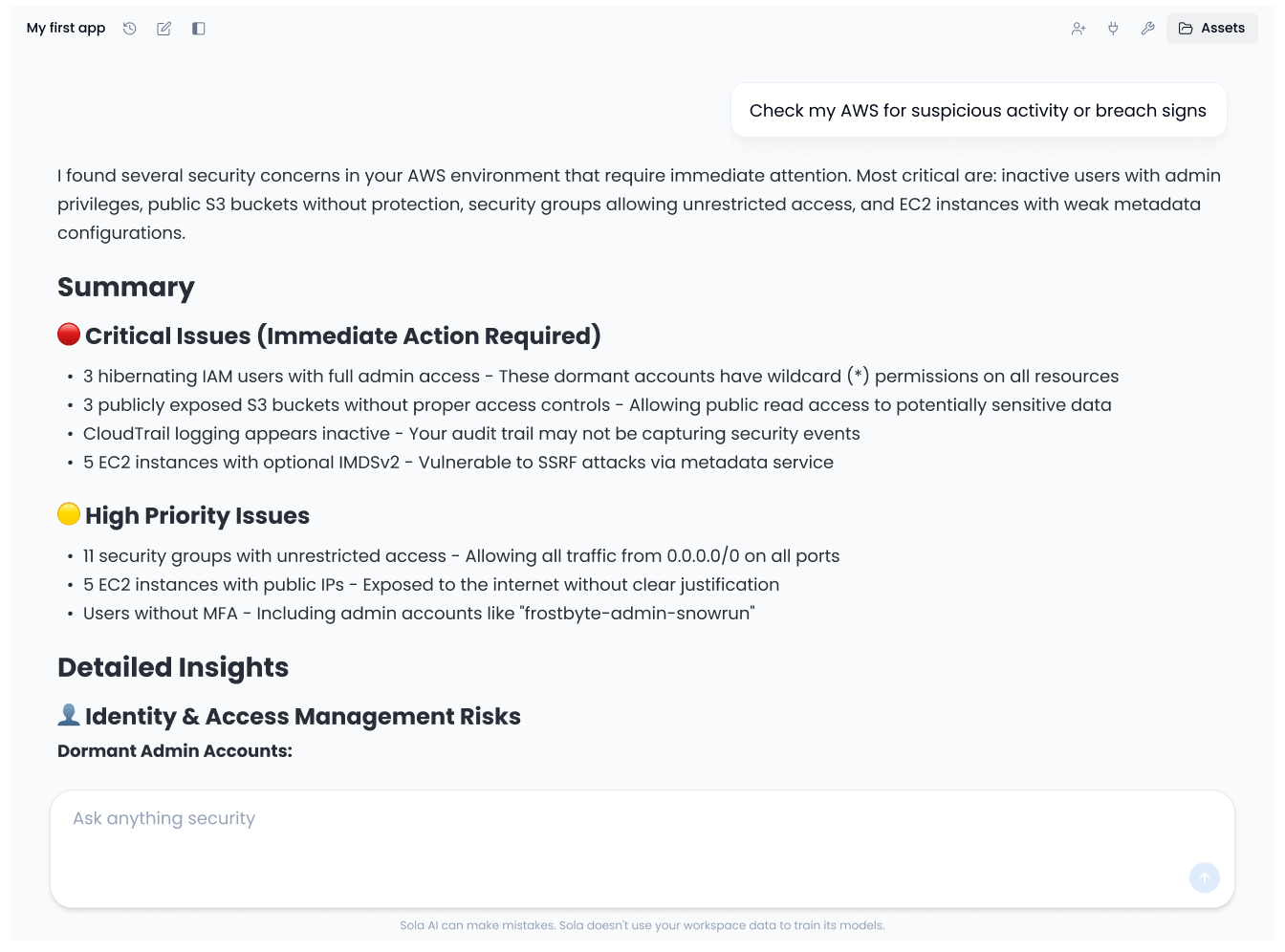
Ask your identity and access questions
Query your entire identity environment in plain language. Try "Show me all service accounts with admin access that haven't been used in 90 days." Get structured answers with queries you can inspect and edit.
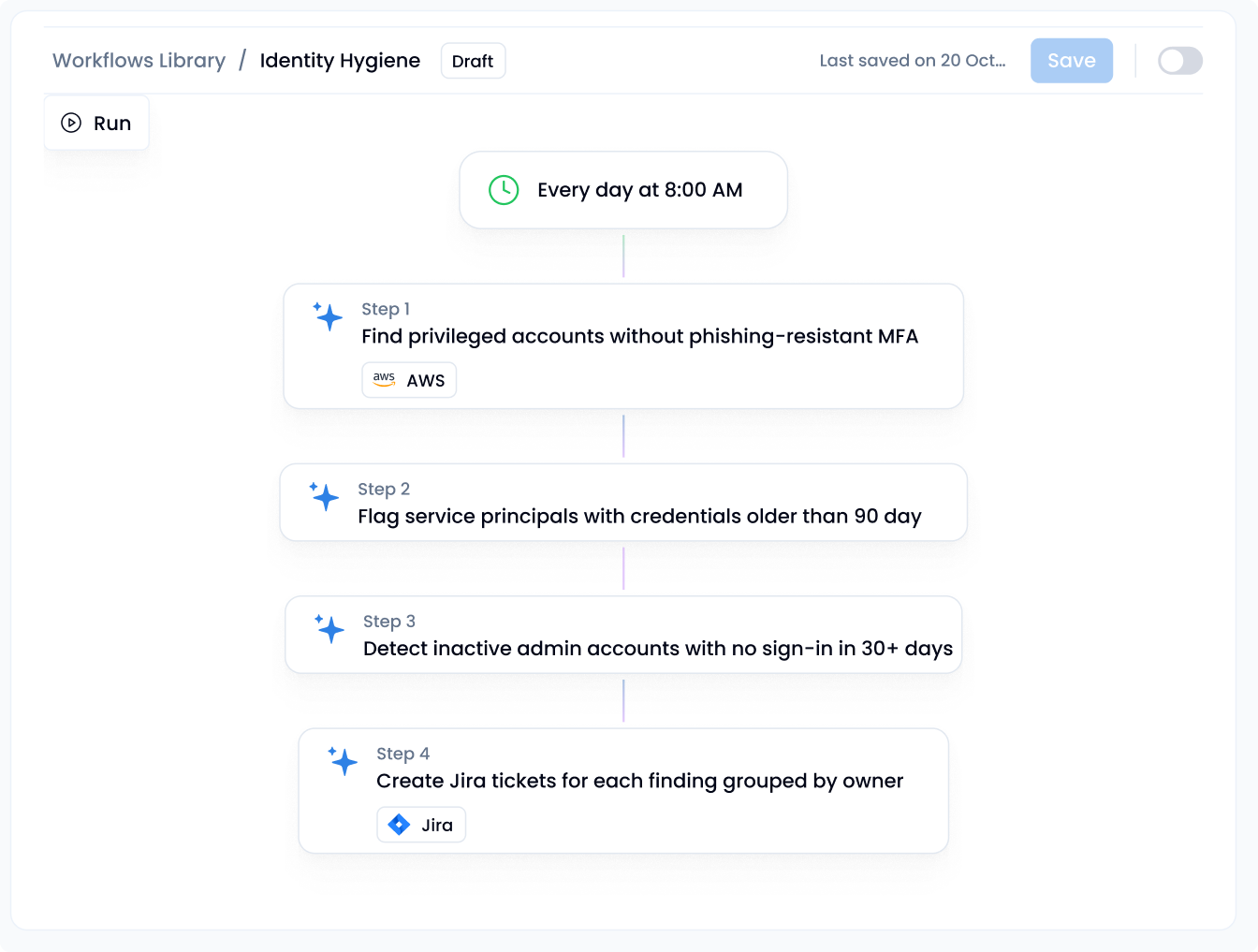
Create IAM security solutions
Save any result as a live canvas: privilege reviews, orphaned account reports, hygiene dashboards. Add workflows and alerts that keep running, so you're not starting from scratch next quarter.