TL;DR
- New CISOs face challenges like lack of visibility, limited resources, and slow time-to-truth in their first week.
- AI in cybersecurity enables quick, evidence-backed answers by mapping identities and assets across systems.
- A security program’s value is measured by its ability to reduce business risk, not just compliance.
- Foundations include a single truth layer, impact-first view, minimum telemetry, shareable evidence, and continuous verification.
- Sola’s AI tool connects data sources to provide immediate cross-system insights and assign ownership for fixes.
- Week one wins focus on producing facts, reducing time-to-truth, and building alignment with named owners and risks.
You walk in as the first security leader. There is no map, just cloud accounts, SaaS everywhere, contractors, and a calendar invite that simply says “make it safe.”
Rule #1: A security program’s value is measured by how much it reduces business risk. If it doesn’t lower likelihood or blast radius against customers, revenue, or regulated data, it’s merely decoration.
The first step in any security program is truth: inventory what you have, map who can reach it, and flag the data that matters. Each stack is unique, so the gaps vary: HR and IdP out of sync, admin creep, SaaS tokens that never die, or vendors and consultants’ over-permissive access. Aim effort where risk falls fastest.
Although SaaS Security Posture Management (SSPM) tools offer strong posture snapshots and policy libraries, most of them struggle with real time, day-to-day usage exposure, such as tracking who shared what or who exported data yesterday. This guide will focus on the practices first; the trade-offs of SSPM tools will be discussed later.
This article is about getting there fast and removing the obstacles that slow new CISOs down. The adoption of AI in cybersecurity makes the difference: impact in days, not months.
Day-one CISO challenges
A new CISO never gets a clean slate; you inherit a running system with gaps. Week one isn’t about vision decks; it’s about facts: what’s out there, who has access, and where the sensitive data lives.
But in reality, it rarely works that way. Even routine questions like “which accounts are in scope and who owns them?” trigger evaluations, approvals, integrations, and DIY scripts. Meanwhile, leadership expects a plan and auditors expect evidence.
Here are some of the challenges CISOs usually face when they enter a new organization:
- Visibility. You can’t start planning without knowing what’s in front of you, whether it is cloud and SaaS assets, opaque identities, or undiscovered data stores. In some cases, logs are either missing, fragmented or impossible to correlate. In other words, lots of noise but little truth.
- Resources. Small team, tight budget, and tools priced like you print money. Each integration adds overhead, context‑switching kills momentum, and you’re navigating between five consoles to assemble one answer.
- Time‑to‑truth. The real cost is time. Weeks vanish into POCs, procurement, security questionnaires, and Platform change windows before the first query runs. Each dependency pushes the schedule out. When the tool is finally in place, you are still assembling the baseline.
- Continuous verification. One-time cleanups decay fast. Systems change, integrations appear, people move teams, and access creeps back. Without a feedback loop, yesterday’s “fixed” becomes tomorrow’s blind spot.
- No cross‑system truth. Valuable questions cross HR, IdP, SaaS, cloud, or GitHub, and never live in one system. “Who was terminated in HR but is still active?” “Who are the admins across IdP, cloud, and SaaS?” “Who can reach critical data and how?” Answering these means stitching exports by hand: brittle, one-off work that can’t be repeated or trusted over time.
Net result: you need quick wins and immediate answers, while inventory is still a guess. Until time‑to‑truth is fixed, plans are just slides.
How AI flips the script (and what you actually need)
AI in cybersecurity is more than a chatbot bolted onto a SIEM. It lets you ask normal questions while it does the ugly work: enumerates systems, maps identities across platforms, joins mismatched schemas, follows access paths, and returns answers with provenance. It handles the mess so you get a single defensible answer.
That collapses time-to-truth. Discovery stops being a project and becomes a loop. You can build a living baseline the same day, then keep it honest with scheduled rechecks. The outcome is not another dashboard; it is an evidence-backed view you can share with owners, with enough context to rank by business impact: who can reach what, how, and from where. Once the facts show up quickly and stay fresh, prioritization changes. You stop spreading effort evenly and start fixing the risks that actually matter.
Foundations that actually matter
- Single truth layer. Normalize identities, assets, data stores, and relationships so that user, service account, repo, bucket, workspace, and role are first class and comparable. Without that foundation, every answer is a one off.
- Impact-first view. Start with what could hurt the business and plan in reverse. Rank everything by reachability, blast radius, and exposure, not by which tool screams the loudest.
- Minimum viable telemetry. You do not need every log on day one. You need the basic evidence that proves who did what, where, and when. Light up what is missing and stop there.
- Insist on shareable evidence. Answers should carry provenance and be trivial to hand to IT, DevOps, or data owners, as well as to senior management.
- Continuous verification. Schedule the questions that define safety so drift in access and posture is caught early, with deltas you can show.
Choosing the AI tool (without building a Rube Goldberg machine)
You have three broad options for adopting AI as part of the onboarding. You can open the generic LLM near you (if you trust it not to hallucinate), but you’ll manually upload spreadsheets and it will still lack your environment’s context.
If you DIY your AI tool using an MCP to achieve more context, you own the plumbing, schemas, scopes, and upkeep. It scales your maintenance burden, so good luck doing that in your first week.
You want AI that reduces time‑to‑truth and carries context across systems, not a connector zoo. That’s where Sola comes in.
How Sola fits
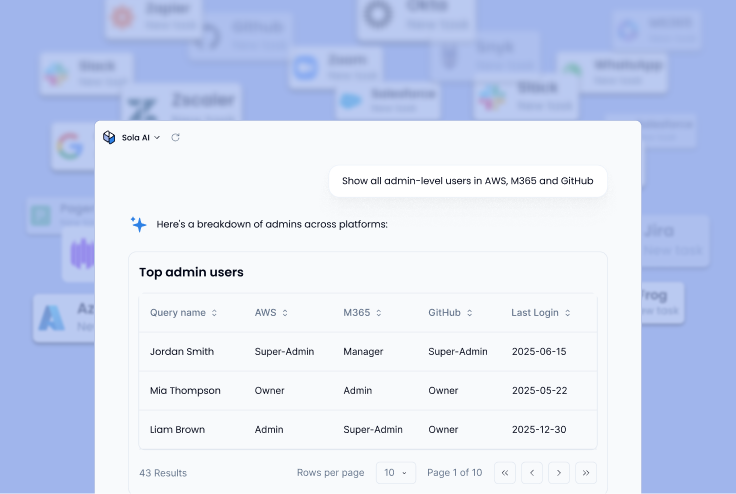
Once you connect your data sources to Sola, you can immediately ask cross-system questions that actually matter for your initial assessment. A couple of examples:
Alternatively, you can use gallery apps for hygiene, SaaS exposure reviews, cloud IAM drift, and OAuth risk, or build exactly what you need.
No matter which path you choose, Sola turns answers into owners and designated tasks, so fixes do not stall. From week one, you have a living baseline and weekly deltas you can share with additional stakeholders. As a new CISO, you can point to what changed, who is on the hook, and what is next.
Benefits you can show this week (not in 6–8 months)
Week one is about producing facts, not promises. You need a defensible picture of assets and access, a short list of risks tied to the business, and named owners moving work forward. The win is time-to-truth and momentum you can act on, not a future-state slide.
- Cut time-to-truth to the minimum. Within minutes, you start to understand your organization’s posture. You’re able to immediately build a current baseline of identities, assets, and data paths that you can trust and reuse, rather than stitching fragmented data pieces from multiple sources.
- Build alignment fast with facts, not roadmaps. Walk into the first executive update with evidence, a clear baseline of what changed, who owns what, and what’s next. That creates buy-in and credibility across the teams that matter; leadership, Platform, and IT, so execution isn’t stuck.
- Focus where it matters (customer data, billing, regulated stores). Point effort at crown jewels first, based on your risk assessment. Suppress noise from the get-go, so teams spend time on issues that can actually impact customers, revenue, or regulated data.
- Make it repeatable. Turn day-one questions into scheduled checks so drift in access and posture is caught early. Fixes stick because the verification loop keeps running.
- Save key resources. No consultant army required, and you don’t need to commit to expensive, bloated tools straight away. Connect the systems you already run, use packaged apps where they fit, and add custom queries only where needed. The tooling supports a small team that needs outcomes now.
In practice, this means you have a living baseline, clear priorities, and owners within the first days of your onboarding. You can brief leadership with measurable progress, not promises, as work continues without the burden of a long POC.
CISO onboarding plans (pick your track)
This is not a grand transformation plan. It is a practical, crucial step towards building a security program grounded in clarity. Pick the track that matches your riskiest unknowns and keep a simple cadence. Focus on the riskiest unknowns, whether it’s identity, cloud, SaaS, or third-party access, and use a “Crawl, Walk, Run” model:
- Crawl: Learn your environment. Build an inventory of systems, identities, or data so you know what actually exists.
- Walk: Analyze and understand your risk. Connect context — who can reach what, what matters most to the business, where exposure lives.
- Run: Act with precision. Prioritize mitigation, assign ownership, and establish controls that stick.
This approach should keep scope honest and turn visibility into control. Here are some suggested tracks, which should be prioritized based on your organization’s needs:
Track A: Identity and access hygiene
Crawl: Connect your IdP (such as Okta), HR platform, and top SaaS tools. Then build an identities and privileges map: all admins (with MFA), HR‑terminated but still active accounts, and dormant accounts/tokens. To cap your first steps, share your generated executive summary (scope, owners, next steps).
Walk: It’s action time: using agentic workflows, route ownership through Slack or Jira. Stand up a quarterly access review skeleton, and clean up groups and rules. Keep drift checks running on schedule.
Run: Track your mean time to closure with weekly reports. Attest access to critical systems and codify least‑privilege principles for admin roles.
Track B: Cloud and data blast radius
Crawl: Connect your cloud providers and data platforms to Sola and inventory buckets, datastores, and snapshots. Flag public or cross‑account exposure and map which users or services can reach sensitive data paths.
Walk: Turn findings into controls (new public objects, wildcard roles, cross‑region drift). Assign owners with context and fix steps. Schedule weekly drift checks and publish a simple weekly delta to engineering and leadership.
Run: Add guardrails for recurring misconfigs. Add data-access attestation for critical stores. Track blast-radius reduction with an automated weekly scorecard.
Other plug-and-play tracks
- Reduce SaaS admin & OAuth sprawl: cut redundant admins, fix sharing defaults, clean up excessive scopes, and review grants continuously.
- Lock down Dev and GitHub posture: secure org secrets, rotate deploy keys, enforce branch protections and required reviews, and fix token hygiene.
- Govern third-party and vendor access: scope external identities, time‑box access, require attestations, and auto‑expire accounts.
Key takeaways
Quick wins beat big promises. Using AI-based discovery and automation, new CISOs can ship proof in week one and keep the loop running.
- Time-to-truth wins onboarding. You need a cross-system truth engine that answers questions fast, not another quarter-long POC or brittle scripts.
- Start where the business bleeds. Map who and what can reach customer and regulated data, billing, and other critical systems. Contain those paths first; everything else can wait.
- With Sola, you move quickly from visibility to action. Connect sources, ask cross-system questions, route fixes to owners, and see weekly deltas. That gives you an exec-ready 30-60-90 plan, and a live baseline you can adapt as risks and priorities evolve.
- Make it continuous. Snapshots rot. Turn week-one queries into always-on checks with ownership, alerts, and workflows that keep fixes from decaying.
Cut your time-to-truth to minutes, not months.
Connect your source, get answers.
Frequently asked questions
Chief Information Security Officer, Sola Security
Yoni has spent the past decade leading security engineering at companies like Meta (formerly Facebook) and AppsFlyer, and now brings his sharp eye and steady hand to Sola as CISO. Known for phishing drills so sneaky they make the real attackers take notes, he stays chill even when everyone else is refreshing dashboards and reaching for incident snacks.