Cloud security answers, in minutes
Sola connects your AWS, Azure, and GCP environments into one queryable workspace. Ask about misconfigs, permissions, or compliance gaps in plain language and get prioritized answers with owners, blast radius, and next steps. Save any result as a live app that tracks drift and alerts you automatically.
Cloud security, the Sola way
Move fast from cloud noise to action, using what you already have: Connect clouds and identity, ask in plain English, get answers you can edit, turn them into live apps, and automate with approvals.
Fix misconfigs, fast
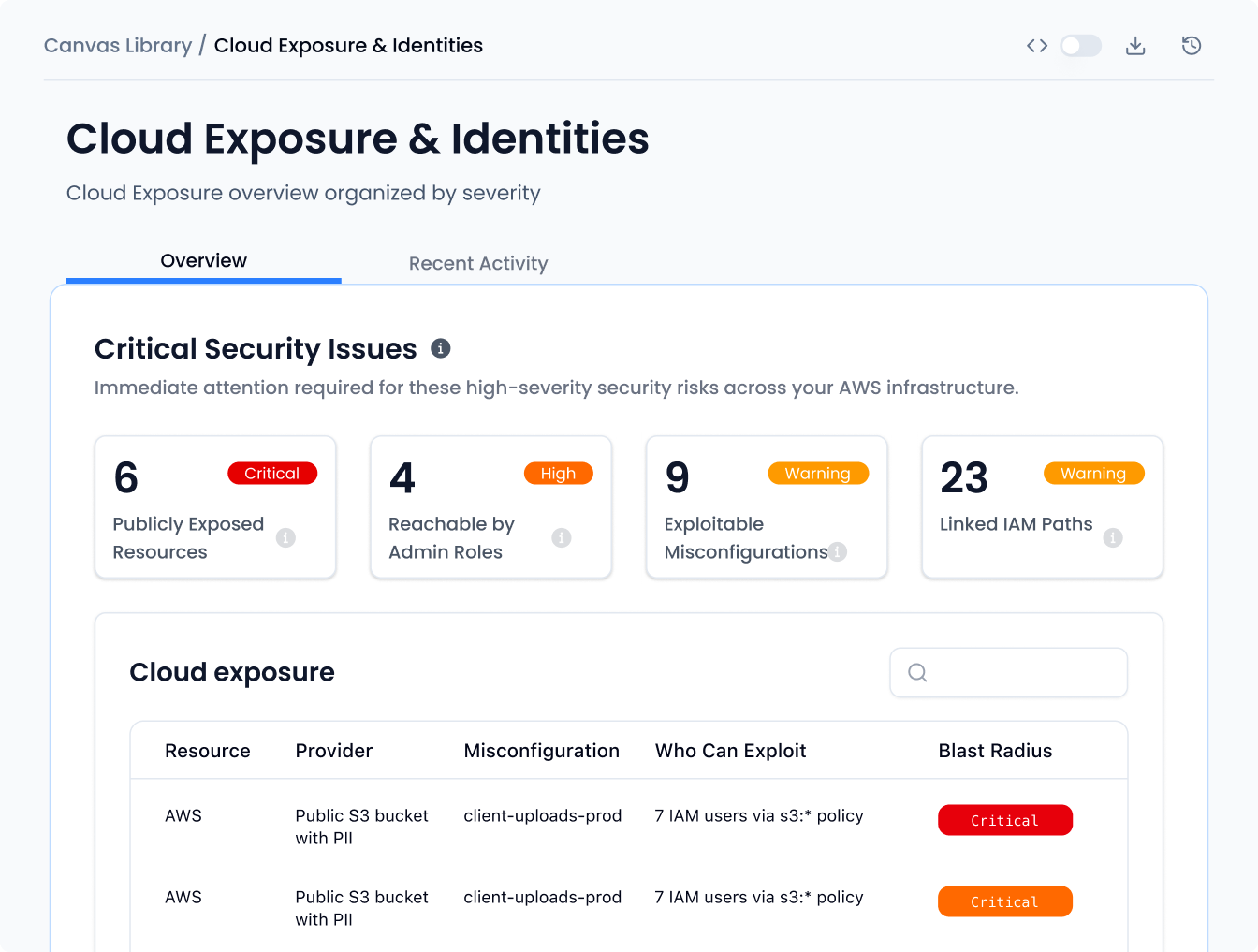
Unify multi‑cloud posture
Enforce least privilege
Triage incidents faster
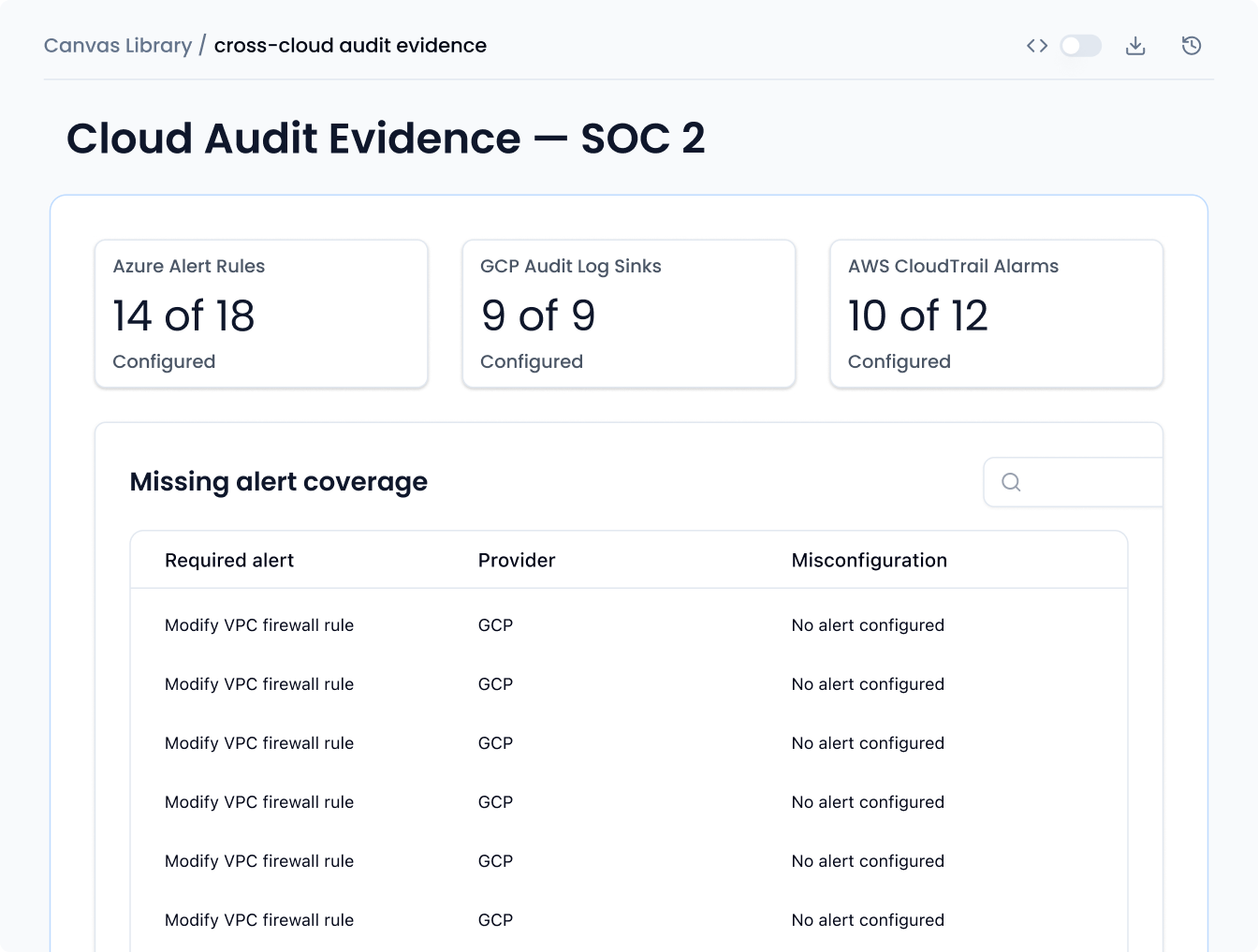
Generate compliance evidence
Prompts to get you started
How Sola works:
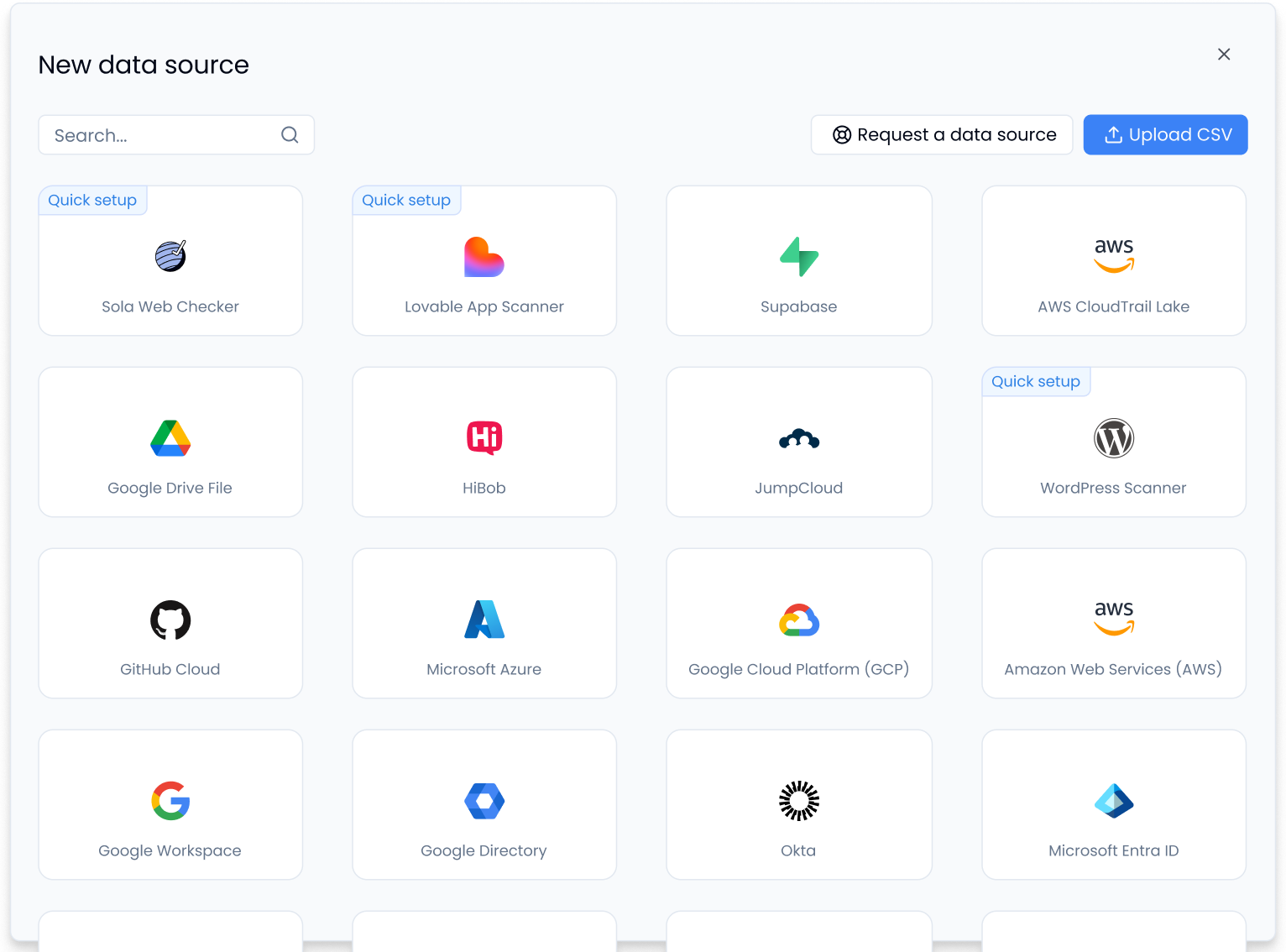
Connect your environments
Link your AWS, Azure, and GCP accounts, projects, and subscriptions in minutes. Sola ingests cloud configs, IAM roles, and activity logs across your stack. Everything lands in a normalized data layer built for cross-cloud security queries.
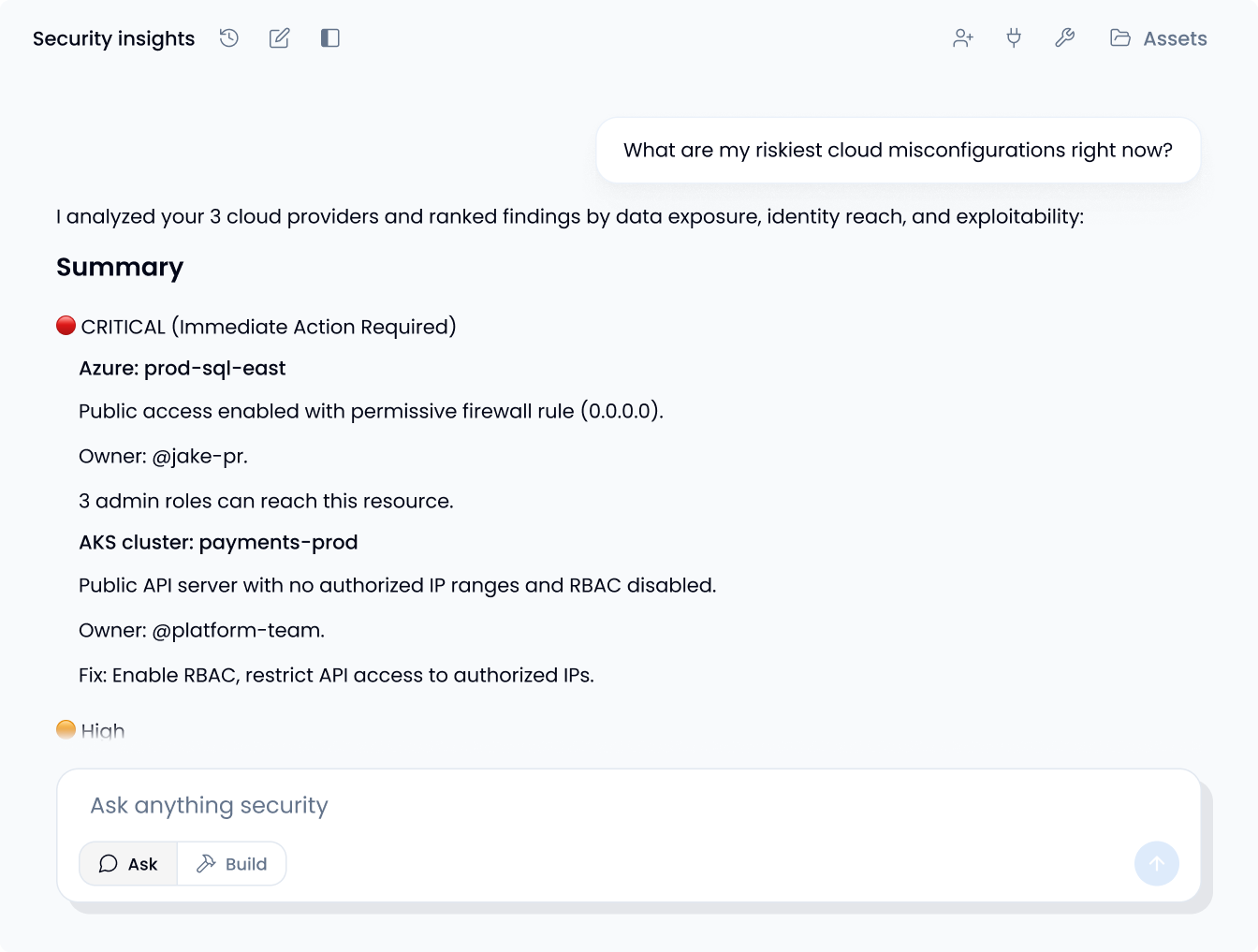
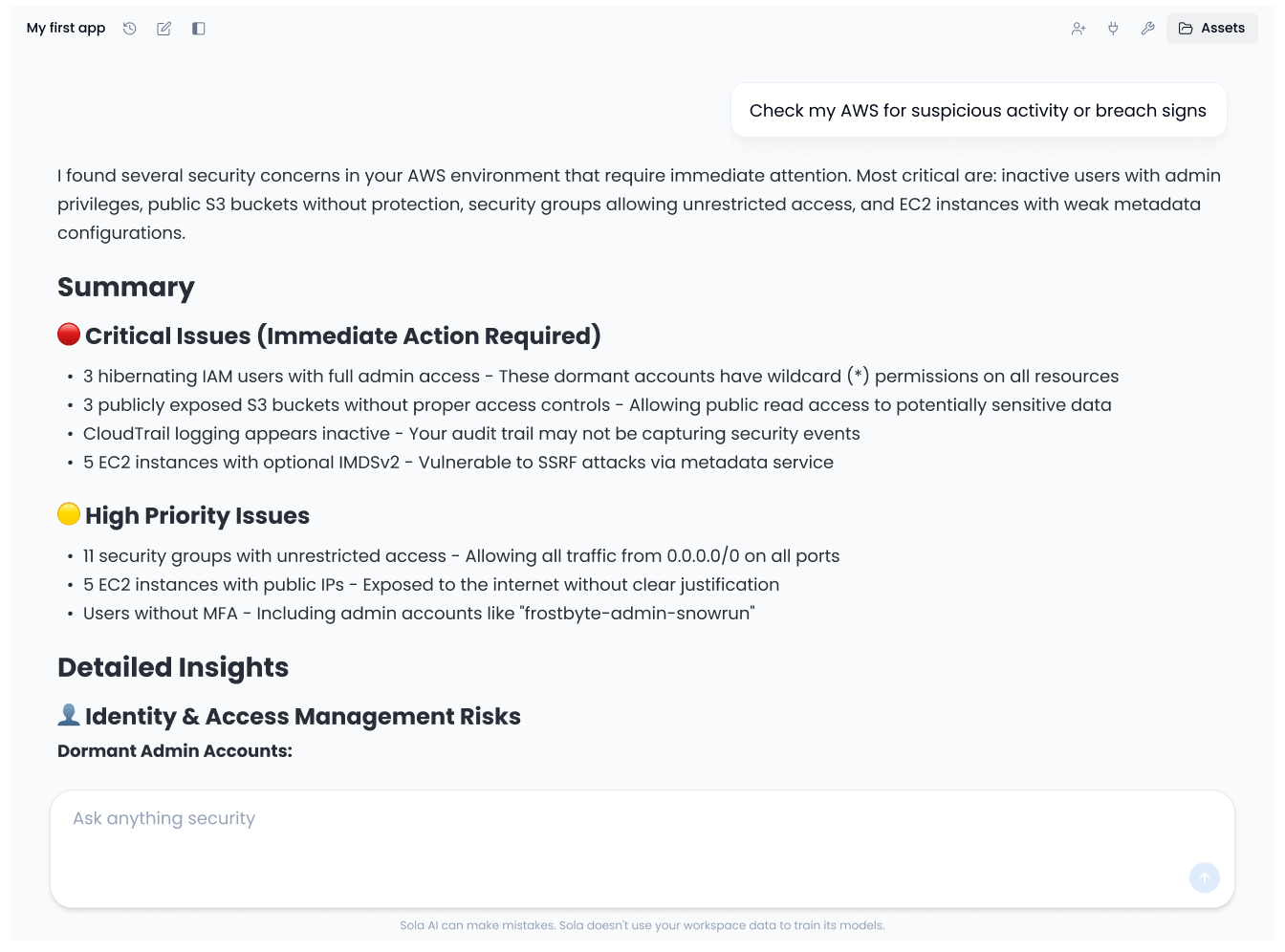
Ask your key cloud questions
Query your environment in plain language. Try 'What are my top 5 risks in AWS?', 'Which public buckets are in prod and who can access them?', or 'Show me roles with admin permissions unused in 90 days.' Get structured answers with queries you can inspect, edit, and refine
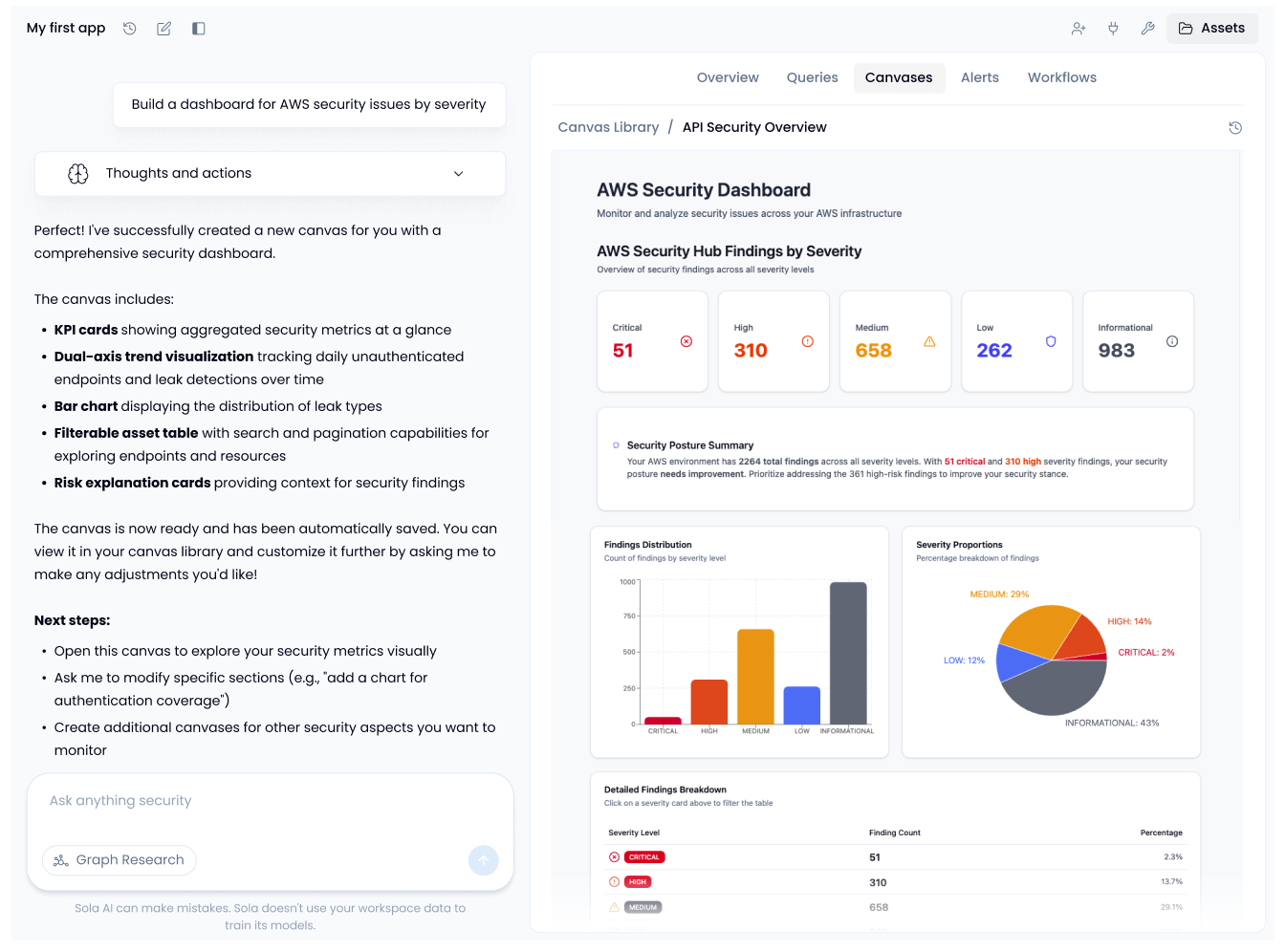
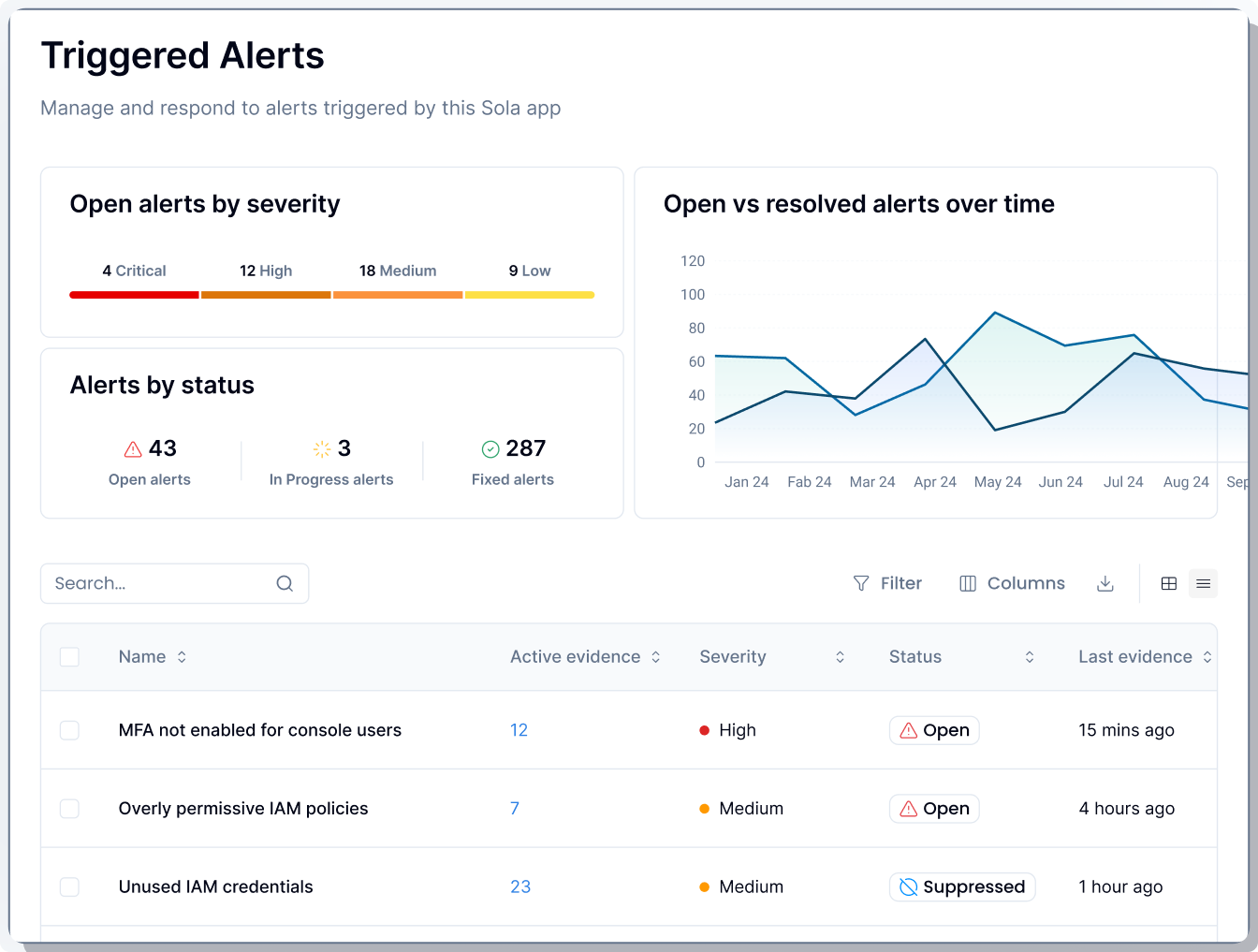
Create cloud security apps
Save any result as a live canvas: posture views, least privilege reviews, drift trackers, or compliance dashboards. Add alerts and workflows that run on schedule with permission controls, approval gates, and full audit trails. Your cloud security keeps working even when you're not watching.